The Invisible Threat of Polymorphic Malware
Polymorphic malware has become a premier risk to the modern enterprise, leveraging constant mutation and AI to bypass traditional signature-based defenses. This course examines the evolution of these threats - from early mutation engines to current malware-as-a-service platforms - and their impact across ransomware, botnets, and phishing campaigns.
Executives and security leaders will analyze why conventional controls fail against sophisticated tactics like sandbox evasion and automated A/B testing. We focus on high-level defensive strategies, including AI-driven threat response, behavioral analysis, and continuous security validation. By evaluating real-world attack data, participants will gain the strategic insight necessary to transition from reactive to proactive security. Ultimately, you will understand how to evolve your organization's posture to effectively mitigate the risks of today’s dominant attack methodology.
Executives and security leaders will analyze why conventional controls fail against sophisticated tactics like sandbox evasion and automated A/B testing. We focus on high-level defensive strategies, including AI-driven threat response, behavioral analysis, and continuous security validation. By evaluating real-world attack data, participants will gain the strategic insight necessary to transition from reactive to proactive security. Ultimately, you will understand how to evolve your organization's posture to effectively mitigate the risks of today’s dominant attack methodology.
Earn 1.5 CPE Credits
Facilitated By:
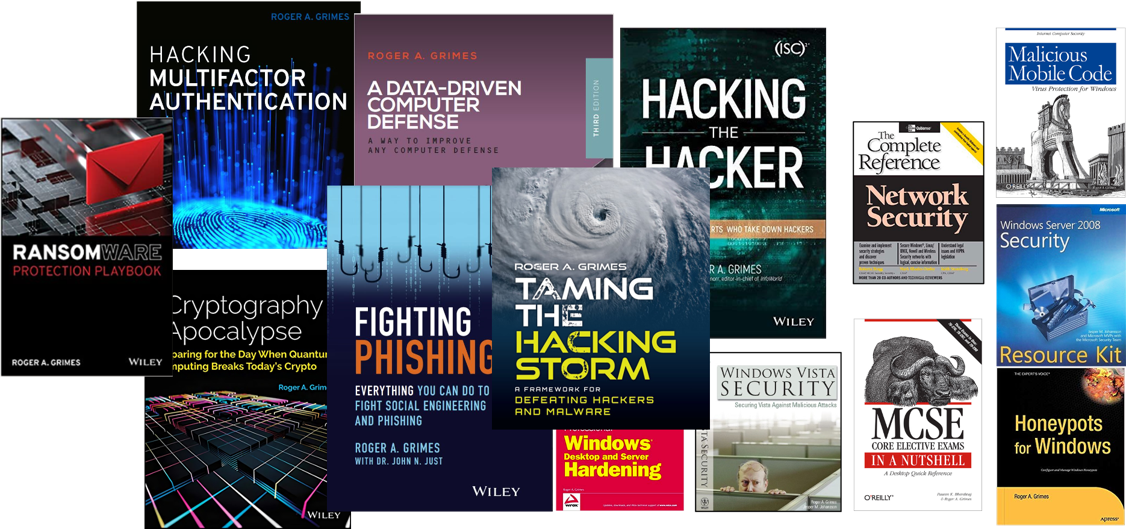
Roger Grimes